Today is the last day of the year of 2015 and we are publishing a summary of top cyber security events that took place in this year.
1. Ashley Madison Hack
Ashley Madison was the most influential security breach of 2015. Why? Because it affected private lives of millions of people. Almost every user of this ‘cheating website’ was interested NOT to find themselves in the database dump. Another reason is that the company was making money by offering users to remove their profiles from the database. Money was taken but the database has never been cleaned!
Related articles:
http://securityzap.com/how-to-download-ashley-madison-dump/
2. Hacking Team Hack
What is more hilarious than watching a hacking group getting hacked? Surfing massive database dump of a hacking group, which was illegally working with repressive governments and was helping them to spy on its citizens. Hacking Team was even offering a service to governments to place child pornography materials on journalists computers.
Related Articles:
http://securityzap.com/how-to-download-hacking-team-torrent-database/
http://securityzap.com/hacking-team-client-list/
http://securityzap.com/hacking-team-boeing-cyber-weapon-drone/
http://securityzap.com/all-anti-hacking-team-patches/
http://securityzap.com/hacking-team-malware-inserts-child-pornography/
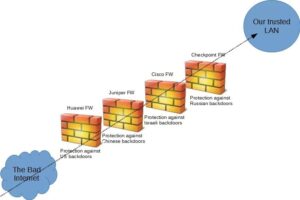
3. Juniper Backdoor
Did you know that it is possible for a leading network device to run for more than three years with a hidden backdoor? Well, this happened to Juniper Networks. Juniper’s own Netscreen Firewall, network equipment that is used to secure Governmental institutions, privately held companies, and intelligence agencies around the world, appeared to have two backdoors for as many as 3 years. Who to blame? NSA?
Related Articles:
http://securityzap.com/juniper-backdoor-what-did-really-happen/
4. The Year of Hacking Cars?
Renown security researcher and car hacker Charlie Miller and Chris Valasek have conducted a demo to Wired’s Andy Greenberg. Hackers gained full access to entertainment system and then rewrote the firmware allowing them to send any commends: transmission, brakes, steering, and more. Will the car hacking ‘trend’ continue in 2016? We will be first ones to publish related information.
Related Articles:
http://securityzap.com/car-hacking-chrysler-hack/
5. Massive Deep Web Links
In 2015 we published the biggest Deep Web Link Directory on the open web that the internet has ever seen. Our users were able to research the deep web, find relevant information for research papers and identify the risks connected to the dark (not darkest) side of the internet.
Related Articles:
http://securityzap.com/massive-deep-web-links-2015-updated-june-2015/
http://securityzap.com/deep-web-links-directory-with-categories/