Zero-day vulnerabilities are security flaws in software or hardware that malicious actors can exploit to gain access to systems and networks. Such vulnerabilities can be extremely difficult for organizations to detect and properly address, as they don’t have time to develop a patch or other solution prior to the attack.
In this article, we will discuss what zero-day vulnerabilities are, how they affect us, different types of zero-day vulnerabilities, how to identify them, and ways to protect against them. We will also explore the role of security experts in mitigating such risks and the various benefits of conducting zero-day vulnerability testing.
Key Takeaways
- Automated scanners and log analysis help uncover and identify zero-day vulnerabilities.
- Patch management is crucial in protecting systems from exploitation by zero-day attacks.
- Employee training on cybersecurity best practices can help reduce the risk of zero-day exploits.
- Zero-day vulnerability testing helps identify weaknesses and implement prevention techniques to protect against known and emerging threats.
Definition of Zero-Day Vulnerabilities
A zero-day vulnerability is a type of computer security flaw that is unknown to the software vendor and can be exploited by attackers before the vendor becomes aware of it. Such vulnerabilities have become increasingly common in recent times due to their ability to provide easy access to sensitive data or system resources without authorization.
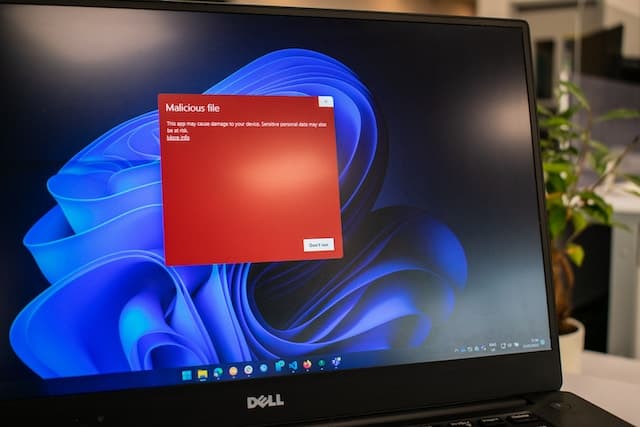
In most cases, attackers target zero-day vulnerabilities with malicious code, such as malware or ransomware, for financial gains. To minimize the risk of exploitation, organizations must develop patching strategies that prevent attacks from exploiting these security flaws.
In order to identify and address potential zero-day vulnerabilities, organizations must carry out regular malware analysis on their systems. This involves assessing suspicious files and programs for any signs of malicious behavior. Additionally, they should also keep track of any new publicly disclosed vulnerabilities in order to ensure that their systems are up-to-date with the latest security patches. Moreover, they need to invest in technologies such as network monitoring and intrusion detection systems which can detect intrusions caused by exploiting these vulnerabilities in real time.
Organizations should also prioritize training and awareness programs for both technical personnel and end users in order to reduce the risk associated with zero-day exploits. These programs should focus on teaching users how to recognize potential threats as well as best practices for secure computing activities.
By taking all necessary precautions against zero-day exploits, organizations can protect themselves from attack vectors that may otherwise go unnoticed until it’s too late.
How Zero-Day Vulnerabilities Affect Us
The exploitation of security flaws before they are publicly known can have serious repercussions. Zero-day vulnerabilities, which refer to unknown, unpatched computer system vulnerabilities that hackers can exploit, are one such example. Such threats pose a significant risk due to their lack of awareness and patching ability.
Zero-day exploits require a high level of technical expertise and resources in order to identify them and develop an exploit. Those who are aware of the vulnerability often use it for malicious intent or illegal activity, leaving the vulnerable system open to attack from outside sources. As the threat of zero-day vulnerabilities grows, so does its legal implications in terms of responsible disclosure and data breaches.
Organizations need to be increasingly vigilant when it comes to identifying potential zero-day threats as they can easily become victims of malicious actors that want access to confidential data or cause disruption. The most effective way organizations can protect themselves is through threat awareness by keeping up with the latest cyber security trends and implementing necessary technologies such as antivirus software and firewalls. Furthermore, organizations should also ensure their systems are patched regularly with the latest updates from vendors in order to prevent attacks exploiting known flaws before they take place.
In summary, zero-day vulnerabilities present an ever increasing risk for organizations due to their lack of awareness and patching ability as well as malicious actors taking advantage of these weaknesses for nefarious intentions; however, organizations can mitigate these risks by staying informed on emerging threats and implementing proper security measures against potential exploits.
Types of Zero-Day Vulnerabilities

Zero-day vulnerabilities, which are previously unknown software security flaws, can have a major impact on the safety and security of computer systems.
Broadly speaking, there are three types of zero-day vulnerabilities: remote code execution vulnerabilities, privilege escalation vulnerabilities, and cross-site scripting (XSS) vulnerabilities.
Remote code execution occurs when an attacker takes advantage of a vulnerability in an application or system to execute malicious code remotely; these attacks can be used for data theft or to gain access to sensitive information.
Privilege escalation involves exploiting weaknesses in software or hardware configurations to gain unauthorized elevated privileges on a system; this allows attackers to bypass normal authentication processes.
XSS is a type of attack that injects malicious code into existing applications in order to steal user credentials or hijack sessions.
Remote code execution vulnerabilities
Remote code execution vulnerabilities involve the exploitation of a security flaw in order to execute malicious remote code on a target system. These types of attacks typically take advantage of unpatched software, and often carry malicious payloads. Attackers will use code injection techniques to gain access to a system and execute arbitrary commands or upload files. In addition, attackers may also be able to modify data or bypass authentication processes.
To better protect against these types of threats, organizations should regularly patch their software and systems with the latest updates, monitor user activities for any suspicious activity, and ensure that only authorized personnel can access sensitive information. Additionally, developers should use secure coding practices such as input validation when creating applications to reduce the risk of code injection attacks.
In summary:
- Unpatched Software is vulnerable to Remote Code Execution Attacks
- Malicious Payloads are used in Code Injection Techniques
- Organizations must Ensure Security through Patches, Monitoring & Authorized Access
Privilege escalation vulnerabilities
Privilege escalation vulnerabilities refer to security flaws that allow an individual with limited access to gain higher-level permissions on a system. These vulnerabilities are typically caused by weaknesses in authentication, authorization processes, or lack of system hardening.
Malware infiltration is also a common vector for privilege escalation attacks, as malicious actors can use the access granted by the software to gain further access and privileges on the system.
To reduce risk from these vulnerabilities, organizations should implement strict policies and procedures related to authentication and authorization, as well as deploy measures such as patching systems regularly and strengthening configuration settings.
Additionally, continuous monitoring of user activity can help identify malicious attempts at privilege escalation before they become successful.
Cross-site scripting vulnerabilities
Cross-site scripting (XSS) vulnerabilities are security flaws that enable attackers to inject malicious code into web applications. XSS attacks involve exploiting the trust a user has for a website by introducing malicious scripts into it, which can be used to:
- Steal confidential information from the website, such as usernames and passwords, or credit card information.
- Redirect users to malicious websites by exploiting browser vulnerabilities or by executing malicious scripts.
- Execute arbitrary code in the context of the vulnerable website, allowing attackers to perform various malicious activities like data theft or denial of service attacks.
Therefore, protecting against XSS vulnerabilities is essential for maintaining an application’s security posture and preventing serious damage from being done by attackers.
Identifying Zero-Day Vulnerabilities

Identification of Zero-Day Vulnerabilities requires an understanding of the associated risks to the system or networks. To accurately identify these security flaws, organizations need to implement a variety of vulnerability scanning techniques and patch management systems.
Security professionals use automated scanning tools to detect vulnerabilities in their networks by comparing the current known security patches with those that are currently installed on their systems. This process allows them to identify any missing or outdated patches which could indicate a possible zero-day vulnerability.
In addition, manual testing can be used for more complex issues such as application or operating system flaws that may exist but have not yet been discovered by automated scanners. By analyzing logs and identifying patterns in user behavior, they can also uncover previously unknown threats.
Patch management is another essential component of identifying zero-day vulnerabilities as it ensures that all systems are up-to-date with the latest security patches and reduces the risk of exploitation from these types of attacks. Through effective patch management strategies, organizations can ensure their networks are protected from both known and unknown threats.
Ultimately, proper identification of zero-day vulnerabilities is essential for an organization’s overall cybersecurity posture as it helps prevent data breaches and other malicious activities from occurring.
How to Protect Against Zero-Day Vulnerabilities
Implementing a comprehensive security strategy is critical for protecting against zero-day vulnerabilities. A key component of this strategy should be prevention strategies, such as regularly scanning the system for any new threats and updating software with the most recent patches. Additionally, patch management is important in preventing zero-day exploits from taking advantage of unpatched systems. It is important to note that patching may not always be successful due to the unpredictable nature of zero-day vulnerabilities, but it still remains an essential part of any effective security strategy.
Another way to protect against zero-day vulnerabilities is by deploying intrusion detection systems (IDS) that are designed specifically for detecting previously unknown malicious activities. These IDS can detect indicators of compromise which are suspicious behaviors or patterns observed on the network that may indicate a breach has occurred or may be imminent. By monitoring these indicators, organizations can quickly respond to potential attacks and mitigate any damage done before attackers have time to take advantage of a vulnerability.
Finally, ensuring that employees are trained on cybersecurity best practices can help reduce the risk associated with zero-day exploits. Employees should understand how their actions affect overall security and be aware of common attack methods used by hackers so they can spot potential issues early on and take action accordingly. Organizations should also ensure that employees know who to contact if they suspect something is wrong as well as how to report any suspicious activity they observe while using company resources or networks.
The Role of Security Experts
Security experts play an important role in protecting against zero-day exploits. They identify potential vulnerabilities and develop effective strategies for mitigation. Their main focus is to create a data-driven approach to security, which provides a comprehensive view of the current cyber landscape. This includes analyzing logs, network traffic, and other data points to identify previously unidentified threats.
Security experts also work on devising ways to protect networks from malicious actors. They monitor suspicious activity and block it before it can cause harm. They are often called upon to respond quickly when a breach has already occurred or when a new vulnerability has been discovered.
In times of cyber warfare, security experts help organizations prepare for potential attacks. They conduct risk assessments and contingency planning to understand the scope of possible risks. This helps organizations handle any eventuality that may arise due to an attack or breach. Security experts also provide advice on securing systems against future threats while maintaining compliance with industry standards such as PCI DSS.
With the increasing complexity of cyber threats and ever-evolving technology landscape, security professionals must remain diligent. Their expertise helps businesses maintain their security posture and protect valuable assets from malicious actors. Without their knowledge and experience, many organizations would be unable to adequately protect their networks from both known vulnerabilities and those yet undiscovered. This makes security experts critical players in preventing successful zero-day exploitations.

Benefits of Zero-Day Vulnerability Testing
Testing for zero-day vulnerabilities provides a range of benefits to organizations. Regular testing helps identify weaknesses in systems and allows for the implementation of prevention techniques to mitigate risk. This proactive approach prepares organizations for possible attacks and helps prevent them from happening in the first place.
Regular testing also gives organizations more insight into their security posture. By accurately assessing potential risks, organizations can prioritize resources effectively and strengthen their defenses in areas with the highest risk of attack. This data can also be used for regular risk assessments, focusing on identifying weak points and developing countermeasures against them.
Conducting regular tests for zero-day vulnerabilities ensures that organizational systems remain up-to-date with the latest security patches and configurations. This protects against known threats and provides protection against emerging ones. These tests also ensure that updates are applied correctly, without leaving any vulnerable gaps or openings for attackers to exploit.
All of these benefits allow organizations to stay ahead of threats while minimizing potential risks associated with new exploits or vulnerabilities.
Tips for Minimizing Risk
Effective risk minimization requires organizations to take proactive steps to ensure their systems are properly secured. To reduce the likelihood of a zero-day vulnerability being exploited, organizations should consider the following steps:
- Developing and implementing a comprehensive patching strategy:
- Establish timelines for patch application across all systems;
- Perform regular system scans to detect any missing patches;
- Automate the process whenever possible.
- Conduct security audits regularly:
- Identify and analyze areas of potential vulnerability;
- Implement solutions that address these vulnerabilities;
- Monitor network traffic for suspicious activity.
- Enforce best practices for data security:
- Restrict access to sensitive information on a need-to-know basis;
- Utilize strong encryption protocols when transmitting data;
- Educate employees on security protocols.
By implementing these measures, organizations can significantly reduce their risks associated with zero-day vulnerabilities and maintain secure data networks.
Additionally, establishing an incident response plan is essential in preparing for successful mitigation of any attack or breach.
Frequently Asked Questions
How can I tell if my system is vulnerable to Zero-Day Vulnerabilities?
To determine if a system is vulnerable to zero-day vulnerabilities, one should consider software patching and vulnerability scanning. Patching reduces the risk of exploitation by installing updates for existing security flaws while scans can detect unpatched vulnerabilities. These methods help identify and mitigate potential threats.
How often should I be testing for Zero-Day Vulnerabilities?
Optimizing security with effective patch management is key to mitigating zero-day vulnerabilities. Regular testing should be conducted to ensure optimal protection against new threats.
What is the most common type of Zero-Day Vulnerability?
Buffer overflow and code injection are two of the most common types of zero-day vulnerabilities. They can have serious implications, as they allow attackers to gain control of systems without prior knowledge or authorization. It is important to understand their potential impact and how to protect against them.
Are Zero-Day Vulnerabilities the same as other types of security threats?
Zero-day vulnerabilities are security flaws or weaknesses in software that can be exploited by attackers to gain unauthorized access. They differ from other threats, such as failing to apply software updates, which do not exploit existing flaws in the system. Zero-day vulnerabilities require exploiting previously unknown software flaws and thus pose a greater risk than other types of security threats.
Can I use my own security measures to protect against Zero-Day Vulnerabilities?
Patching strategies and authentication protocols are effective measures for protecting against security threats. However, it is unclear how successful they may be in preventing zero-day vulnerabilities. Further research is needed to determine the efficacy of these strategies for this purpose.
Conclusion
Zero-day vulnerabilities are a serious threat to security. They can cause significant damage and have the potential for major financial losses, as well as the loss of sensitive data.
To protect against zero-day vulnerabilities, security experts need to be informed about different types of threats and how to identify them, while also understanding the importance of testing systems regularly.
Organizations should put in place measures such as secure coding practices and vulnerability assessments that enable them to respond quickly to any identified issues.
By taking these steps, organizations can help reduce their risk from zero-day vulnerabilities and minimize their exposure to malicious attacks.
