Malware is a type of malicious software designed to gain access to or damage a computer system without the owner’s knowledge or consent. It can range from viruses and worms to Trojans, spyware, ransomware, and other malicious programs.
This article will explore the different types of malware, how it spreads, signs of infection, prevention strategies, and its impact on individuals and organizations.
Additionally, this article will discuss the current state of malware as well as what the future may hold for it.
Key Takeaways
- Malware refers to malicious software that is designed to damage or disrupt computer systems.
- There are various types of malware, including viruses, worms, Trojans, ransomware, and spyware, each with different characteristics and methods of spreading.
- Signs of a malware infection include slow system performance, frequent crashes, unexpected pop-ups, and unauthorized access to personal information.
- To protect against malware, it is important to use antivirus software, avoid suspicious emails and websites, use strong passwords, and regularly back up data.
What is Malware?
Malware is a term used to refer to malicious software that is designed to damage or disable computers and computer systems. Malware can be distributed in various ways, including through email attachments, downloads of corrupted files, and by exploiting vulnerabilities in web browsers and applications. Malware can also exploit social engineering techniques such as phishing scams to gain access to confidential data. Additionally, malware can spread from one computer system to another through networks and removable media.
Once installed on a computer system, malware may remain hidden or become active without the user’s knowledge. It may display intrusive advertising, modify settings or content on the user’s device, collect information about the user without their permission or steal sensitive information such as passwords. Malware can also execute commands remotely which could result in further damage such as disabling anti-malware programs or deleting important files from the system.
Due to its wide range of activities and effects it has on systems and users, malware is considered one of the most dangerous threats in cyberspace today. To protect themselves against malware attacks, users should employ strong security measures such as firewall protection, antivirus software updates and regular patching of vulnerable applications. Additionally, they should exercise caution while browsing online and avoid clicking suspicious links or downloading unknown files sent via email.
Types of Malware
Different computer threats can be classified into various types. Malware is one of the most common and dangerous security risks, which can cause major damage to a system or network. It includes malicious programs that are designed to access, disrupt, modify or steal data without the user’s knowledge.
The following are four main types of malware:
- Viruses: A virus is a type of malicious software that replicates itself by inserting its code into other computer programs and files. It usually spreads through the sharing of infected files over networks or removable media such as USB drives.
- Trojans: This type of malware disguises itself as legitimate software but can perform malicious activities such as stealing data, taking control of a computer’s resources, deleting files or installing other malware in the background without the user’s knowledge.
- Worms: A worm is another form of malware that can spread quickly across networks and computers without any user action required for it to replicate itself; this allows worms to spread more quickly than viruses.
- Phishing Techniques & Social Engineering: These techniques involve using deception tactics to trick users into revealing sensitive information such as passwords or financial details which can then be used by attackers for identity theft and fraud purposes.
Malware has become an increasingly sophisticated threat that requires organizations and individuals alike to take adequate measures in order to protect their systems from being compromised by these malicious programs. Security solutions must be deployed in order to detect and remove any existing threats while also preventing future attacks from occurring on their systems or networks.
How Does Malware Spread?

Understanding how malware is spread is essential for protecting computer systems from malicious attacks. Malware, or malicious software, can be spread through a variety of different sources, including email attachments, social media links, and downloads from malicious websites. It can also be installed on computers by exploiting vulnerabilities in the system. In order to avoid phishing scams and other online threats, users need to remain vigilant when browsing the internet. Additionally, it is important to keep all software up-to-date and disable macros when opening documents sent via email.
Malware can also be distributed using physical media such as USB drives or CDs which contain malicious code that execute once inserted into the computer system. Furthermore, many types of malware use an exploit known as drive-by downloading in which the user unknowingly visits a website containing malicious code which then allows malware to install itself onto their computer without any warning signs or prompts. Finally, some networks are vulnerable to ‘man-in-the-middle’ attacks where hackers inject malicious code into legitimate network traffic in order to gain access to sensitive data stored on connected devices.
It is important for users and organizations alike to understand how malware spreads in order to protect themselves against these dangerous threats. Taking steps such as ensuring anti-virus software is regularly updated and avoiding suspicious websites will help reduce the chances of falling victim to a malware attack. Additionally, educating employees about potential cyber threats can help ensure they know what actions they should take if they suspect their device has been infected with malware.
Signs of Infection
Signs of infection from malware can range from minor system disruptions to major data loss. Detecting the presence of malicious programs on a computer or network requires recognizing certain behaviors that indicate an infection.
For example, if a user notices their browser’s homepage has changed without their consent, this could be a sign of infection as malware often tampers with settings to redirect users to unwanted websites. Another indication is slower computer performance, which could mean the system is being used for unintended tasks by malicious actors.
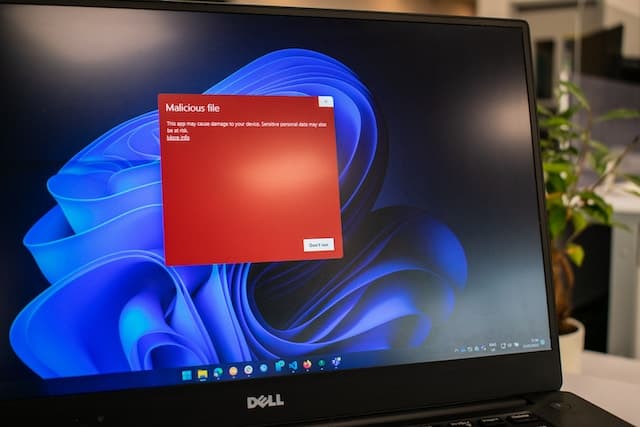
In addition, some viruses may even change file names and locations in order to stay hidden and avoid detection by antivirus software. Furthermore, pop-ups and warnings may appear warning that the system is infected or offering fake updates for software already installed on the device. These are also signs of infection as they are usually generated by malicious programs trying to disguise themselves as legitimate software updates in order to fool victims into downloading them onto their computers.
Malware can also cause other symptoms such as unexpected emails sent out by the user’s account without their knowledge or authorization; this indicates that their email address was compromised in some way. Computer users should also be aware of any sudden changes made on their devices that they did not initiate themselves; these changes might include new desktop icons appearing or unknown files added to folders without permission.
If any suspicious activity is noticed on a computer or device it should be reported immediately so action can be taken against potential attackers before further damage occurs.
How to Protect Yourself from Malware

Protecting oneself from malware is an important step in maintaining a secure digital environment. Taking measures such as installing antivirus software, using strong passwords, and updating software regularly are all effective ways of preventing malicious attacks.
Avoiding suspicious emails and websites is another crucial aspect of protecting against malware. These can often be sources of harmful viruses or phishing attempts.
Backing up data is also a key method of protection. In the event of a malware attack or system failure, having a backup ensures that important files and information can be easily restored.
Practicing these methods of protection can help to ensure a safe and secure system for personal or business use.
Install Antivirus Software
Installing an antivirus program is a recommended approach to protect against malicious software. Antivirus software works by monitoring the computer and its files for suspicious activity, as well as scanning for any known malware signatures.
It also helps detect phishing scams that are designed to steal personal data or install malicious programs on the computer. By using monitoring tools from a reputable antivirus provider, users can be alerted of any malicious activity on their computers, allowing them to take corrective measures in a timely manner.
Furthermore, keeping the antivirus program up-to-date ensures that it is able to detect the latest threats and keep the system secure.
Overall, installing an antivirus program is one of the most effective ways of protecting oneself against malware attacks.
Use Strong Passwords
Using strong passwords can help to reduce the risk of unauthorized access to online accounts. Having secure passwords for all digital accounts is essential in today’s world, as they are often a first line of defense against malware and other cyber threats. Password managers can be used to help generate and store complex passwords that are difficult for hackers to guess. They provide an additional layer of security, making it more difficult for malicious actors to gain access to user accounts.
Furthermore, regularly changing passwords is highly recommended as it helps prevent malicious actors from using previously obtained credentials. It is also important for users to avoid using the same password for multiple accounts, as this increases the chances of a successful attack on at least one account.
Overall, creating complex passwords and using password managers can help keep user data safe from malicious actors looking to exploit vulnerable systems.
Update Your Software Regularly
Regularly updating software can provide important security benefits by helping to protect against cyber threats. It is an essential practice for avoiding scams, patching vulnerabilities, and protecting personal information from malicious actors.
- Benefits of Software Updates:
- Patches security vulnerabilities quickly and effectively
- Provides the latest bug fixes and feature updates
- Allows users to take advantage of security enhancements
- Implementation Resources:
- Automatic updates on all devices used regularly
- Security notifications when updates are available
- Setting aside time to check for missing patches or outdated software
- Considerations for Updating Software:
- Ensure that installed applications are compatible with updated versions
- Be aware of any potential privacy issues resulting from new features or changes in data collection policies
Avoid Suspicious Emails & Websites

Being aware of phishing emails and suspicious websites is essential for avoiding cyber threats.
Modern malware exploits user behaviour by attempting to trick individuals into downloading malicious software or visiting a malicious website. This can be done through deceptive email messages that appear to be from legitimate sources, such as banks, retailers, or even government entities.
As such, users should remain vigilant and avoid clicking on any links within suspicious emails unless they are certain of the sender’s identity and legitimacy.
Additionally, it is important to avoid visiting unknown websites as they may contain malicious content or links designed to install malware onto the device.
By adhering to these simple steps, users can significantly reduce the risk of becoming a victim of phishing scams and other forms of malware prevention.
Backup Your Data
Backing up data is an important step to ensure the preservation of files in the event of a cyber attack. Data backup strategies can help protect against malware and other malicious software, as well as provide an additional layer of security for sensitive information.
The most effective way to back up data is by using encryption, which encodes the files so that only those with access to the decryption key can view it. Other backup strategies include copying files into cloud storage or external hard drives and keeping multiple copies in different locations.
Regular backups should be taken at least once a week to minimize any possible losses due to viruses or ransomware attacks. In addition, online backups should be securely encrypted and passwords changed periodically for added protection.
By following these backup strategies, businesses and individuals can protect their valuable data from malware threats.
What to Do If You Are Infected
If infected with malware, it is important to take immediate steps in order to mitigate the damage. Malware prevention should be a priority for all users, but if an infection has already occurred, there are certain steps that can help contain the damage and protect user data.
First, the source of the malware must be identified and removed. This may require updating or reinstalling corrupt programs or applications.
Next, any malicious files must be quarantined or erased from the system. Malware detection software can also be used to scan a device for malicious software and remove it if found.
Once this is done, users should run regular scans on their system using anti-virus protection software to ensure no further malicious activity occurs on their devices. Additionally, backups of important data should be taken so that the information is not lost in case of a more serious attack or complete system failure.
Finally, password security measures should be implemented and updated regularly to prevent future attacks from taking place. All these steps together will help mitigate any potential harm caused by malware infections and keep user data safe and secure.
The Impact of Malware

The consequences of malware infections can be far-reaching and have a profound impact on individuals, organizations, and society as a whole. Malware is designed to exploit vulnerabilities in computer systems in order to gain access to confidential information or cause disruption within the system.
At an individual level, this could mean the loss of personal data such as financial records or photos. At an organizational level, it could lead to financial losses due to downtime or stolen data being sold on the dark web. At a societal level, malware attacks can have serious implications for national security and public safety.
Hackers often target vulnerable organizations with malicious intent and their motives vary from financial gain to political sabotage. This has led to governments introducing new cybercrime laws in an attempt to tackle malicious activity online and protect citizens from potential threats posed by hackers. These laws aim to deter hackers through providing harsher punishments for those caught engaging in illegal activities online.
For businesses, one of the most effective ways of preventing malware attacks is by investing in cybersecurity measures such as antivirus software and regular security updates which reduce the risk of infection and prevent unauthorized access into networks. Additionally, companies should provide employees with adequate training so that they are aware of common cyber threats such as phishing emails which could potentially lead to malware infections if clicked on or opened without caution.
In summary, malware can have serious repercussions for individuals, organizations, and society as a whole due its ability to exploit vulnerabilities in computer systems with potentially devastating effects ranging from financial losses due to downtime all the way up national security issues caused by malicious actors with unknown motives behind their actions. As such it is essential that steps are taken both at an individual and organizational level in order mitigate these risks posed by malicious software whilst also ensuring compliance with relevant cybercrime laws established by governments worldwide.
The Future of Malware
As technology advances, malware is likely to become increasingly sophisticated and dangerous. It is predicted that the use of artificial intelligence (AI) in malware will grow, allowing cybercriminals to target users more efficiently and launch more complex attacks. AI-based malware can also learn from its environment and adapt itself to evade detection by ransomware protection tools.
In addition, targeted attacks on connected devices are expected to increase, as attackers gain access to sensitive data stored on these devices.
Furthermore, as organizations continue to expand their digital footprints across multiple platforms and channels, they will be exposed to a greater risk of attack due to the increasing complexity of their networks. This could lead attackers to develop new methods for gaining control over these networks or using them for malicious purposes such as exfiltrating data or launching distributed denial-of-service (DDoS) attacks.
The rise in the number of connected devices has also increased the potential targets for malicious actors. Attackers can exploit vulnerabilities in vulnerable IoT devices or deploy malicious code into mobile applications without users being aware. As a result, organizations need to strengthen their security posture by implementing effective security strategies such as patching systems regularly and deploying robust authentication protocols like two-factor authentication (2FA). Additionally, organizations should consider investing in advanced threat prevention solutions that leverage AI-driven analytics for better detection capabilities against advanced threats such as zero-day exploits and lateral movement attacks.
In order for organizations to protect themselves from future threats, they must ensure that they have an up-to-date understanding of the threat landscape so that they can deploy appropriate defense mechanisms against new types of malware before it becomes too late. Additionally, companies must foster a culture of security awareness within their organization so that employees know how best to respond in case a security incident occurs on their network or device.
By taking proactive steps now towards securing their online presence, companies can minimize the risks posed by future threats from malicious actors.

Frequently Asked Questions
How can I check if my device has been infected by malware?
To check if your device has been infected by malware, it is important to take preventative measures such as installing and using reliable malware protection software. Additionally, monitoring your device for unusual activity can help detect any malicious behavior early on.
Is malware a physical threat?
Malware risks can pose a physical threat, as malicious software can be designed to disrupt or manipulate computer systems and hardware. Such threats, if left unchecked, could cause significant damage and financial loss. Therefore, it is important to consider malware as a potential physical risk.
Are there any legitimate uses of malware?
Malware, such as malicious software and other forms of protection, can be used legitimately in certain situations. For example, it may be used for network security or for tracking illegal activities. However, it is important to use malware cautiously and responsibly.
Is there a way to completely remove malware from my device?
Malware prevention and cyber security are key to removing malware from any device. It is possible to detect and remove malicious software by using anti-malware software and regularly updating the operating system. However, complete removal of malware requires long-term vigilance.
Is it possible for malware to steal personal information from my device?
Yes, malware can potentially steal personal information from a device. Cyber security measures should be taken to reduce the risk of attacks, including using anti-malware software and regularly updating security systems.
Conclusion
Malware is a serious threat to our digital security and privacy, and its impact can be devastating. With the increasing number of connected devices, malware will continue to evolve and adapt. As technology advances, so does the sophistication of malware attacks.
To protect ourselves from becoming victims of malicious software, we must remain vigilant in understanding the risks posed by malware, taking steps to prevent infection, and knowing what to do if we do become infected. Taking proactive steps to secure data and networks is essential for staying safe online in the future.
