In the modern era, educational institutions are increasingly turning to cloud services for storing and managing student data. However, this shift towards cloud-based solutions also brings about concerns regarding the security of such sensitive information.
This article addresses the strategies that educational organizations can employ to ensure the protection and confidentiality of student data in cloud services. By understanding and mitigating potential risks, implementing data encryption measures, and adhering to data protection laws, educational institutions can enhance their data security practices and create a secure digital learning environment.
This article also highlights the importance of strong access controls, regular security updates, vendor assessments, user education, data backup and recovery plans, as well as monitoring and detecting suspicious activities. By following these strategies, educational institutions can safeguard student data and promote a safe and secure educational experience.
Implementing Strong Access Controls
Implementing strong access controls is crucial for ensuring the security of student data in cloud services. Cloud data security and student data privacy are of utmost importance in the education sector, where cloud services are widely used. Access controls refer to the mechanisms put in place to regulate and manage user access to sensitive data and resources.
By implementing strong access controls, educational institutions can mitigate the risk of unauthorized access to student data and protect the privacy of their students.
To enhance cloud data security, access controls should be implemented at multiple levels. This includes user authentication and authorization processes, as well as the use of encryption techniques to protect data in transit and at rest. User authentication ensures that only authorized individuals can access the cloud services, while user authorization defines the level of access each user has to the data.
Additionally, access controls should be regularly reviewed and updated to ensure that they align with the evolving security requirements and comply with data protection laws. Educational institutions must also provide training to staff and students on best practices for maintaining the security and privacy of student data in cloud services.
Regularly Updating Security Measures
Regularly updating security measures is crucial in maintaining the integrity and confidentiality of student data stored in cloud services. By promptly applying software updates and patching vulnerabilities, educational institutions can mitigate the risk of cyber attacks and data breaches.
Additionally, implementing proactive security measures, such as intrusion detection systems and threat intelligence, can help identify and address potential security threats before they can exploit any weaknesses in the system.
Importance of Software Updates
Cloud service providers must regularly update their software to ensure the security measures protecting student data are up to date. Software updates are essential for addressing vulnerabilities and patching security holes that could be exploited by cybercriminals. By regularly updating their software, cloud service providers can stay ahead of emerging threats and protect student data from unauthorized access or data breaches.
Software updates also play a crucial role in keeping security measures effective and robust. They often include enhancements to encryption algorithms, improved authentication protocols, and strengthened access controls. These updates help to ensure that student data remains encrypted and inaccessible to unauthorized individuals.
Additionally, software updates enable cloud service providers to comply with data protection laws and regulations. By implementing the latest security measures, they can demonstrate their commitment to safeguarding student data and maintaining compliance with legal requirements.
Incorporating a 2 column and 3 row table in markdown format can help evoke emotion in the audience:
| Benefits of Regular Software Updates | Risks of Neglecting Software Updates |
|---|---|
| Protection against emerging threats | Increased vulnerability to attacks |
| Enhanced encryption and access controls | Potential data breaches |
| Compliance with data protection laws | Legal and regulatory consequences |
Patching Vulnerabilities Regularly
To ensure the ongoing security of student data in cloud services, it is essential to consistently patch vulnerabilities and update security measures. Regularly updating security measures helps to protect against emerging threats and ensures that the latest security patches are applied.
Here are four reasons why regularly patching vulnerabilities is crucial:
- Preventing data breaches: Regular patching closes security loopholes that hackers can exploit to gain unauthorized access to student data, reducing the risk of data breaches.
- Maintaining system integrity: Updating security measures helps to maintain the integrity of cloud systems, ensuring that they are protected against potential vulnerabilities that could compromise student data.
- Complying with regulations: Many data protection laws and regulations require organizations to regularly update their security measures to protect sensitive data, including student information. Failure to do so may result in legal and financial consequences.
- Building trust: Consistently patching vulnerabilities demonstrates a commitment to the security and privacy of student data, helping to build trust with parents, students, and educational institutions.
Implementing Proactive Security Measures
Consistently updating security measures is essential for ensuring the ongoing protection of student data in cloud services. By regularly updating security measures, educational institutions can stay ahead of emerging threats and vulnerabilities. This proactive approach helps to mitigate risks and maintain the confidentiality, integrity, and availability of student data. Implementing proactive security measures involves several key steps, as shown in the table below:
| Step | Description |
|---|---|
| 1 | Conduct regular security assessments to identify vulnerabilities and weaknesses. |
| 2 | Stay up-to-date with the latest security patches and updates for cloud services and applications. |
| 3 | Implement multi-factor authentication to enhance access control and prevent unauthorized access. |
Conducting Thorough Vendor Assessments
Conducting thorough vendor assessments is crucial in ensuring the security of student data in cloud services.
One of the key points to consider is the vendor’s security measures, including their data encryption protocols and access controls.
Additionally, a comprehensive risk assessment process should be conducted to identify potential vulnerabilities and evaluate the vendor’s ability to mitigate them.
Vendor Security Measures
When assessing vendors for the security of student data in cloud services, it is important to thoroughly evaluate their security measures. Here are four key considerations to keep in mind:
- Data encryption: Ensure that the vendor encrypts student data both at rest and in transit. This will protect the data from unauthorized access or interception.
- Access controls: Evaluate the vendor’s access control mechanisms to ensure that only authorized individuals have access to student data. This includes measures such as strong authentication and role-based access control.
- Security audits and certifications: Look for vendors who regularly conduct security audits and hold relevant certifications, such as ISO 27001. These indicate a commitment to maintaining a secure environment for student data.
- Incident response and breach notification: Assess the vendor’s incident response procedures and breach notification policies. It is crucial that they have a clear plan in place to address potential security incidents and promptly notify affected parties in the event of a data breach.
Risk Assessment Process
One crucial step in securing student data in cloud services is to conduct a thorough risk assessment process when evaluating vendors.
This process involves identifying potential risks associated with the use of cloud services and assessing the vendors’ ability to mitigate those risks effectively.
The assessment should consider factors such as the vendor’s security measures, data encryption practices, compliance with data protection laws, and their track record in handling data breaches.
It is important to evaluate the vendor’s security policies and procedures, including access controls, incident response plans, and employee training programs.
Additionally, assessing the vendor’s reputation and financial stability can provide insights into their commitment to data security.
Compliance With Regulations
By ensuring thorough vendor assessments, educational institutions can maintain compliance with data protection regulations when securing student data in cloud services.
To effectively conduct vendor assessments, educational institutions should consider the following:
- Security Measures: Assess the security measures implemented by the cloud service provider, such as encryption protocols, access controls, and intrusion detection systems. This ensures that student data remains protected from unauthorized access.
- Data Handling Policies: Evaluate the vendor’s data handling policies to ensure compliance with regulations regarding data storage, transfer, and deletion. This includes understanding how the vendor handles data breaches and notification processes.
- Contractual Agreements: Review the terms and conditions of the contract with the vendor, ensuring that it includes provisions for data protection, privacy, and compliance with relevant regulations.
- Vendor Reputation: Research the vendor’s reputation in the industry, considering factors such as past security incidents, data breaches, or legal disputes. This helps to gauge the vendor’s commitment to data protection and compliance.
Educating Users on Data Privacy
To ensure the security of student data in cloud services, it is essential to educate users about data privacy. Many cloud services offer robust security measures to protect student data, but users must also understand their role in maintaining data privacy.
Educating users on data privacy involves providing them with knowledge about the risks associated with cloud-based student data and the importance of data encryption in the cloud.
Users should be informed about the potential risks of storing student data in the cloud, such as unauthorized access, data breaches, and data loss. They should understand the importance of strong passwords, multi-factor authentication, and regular updates to minimize these risks. Additionally, users should be aware of the need for data encryption in the cloud, which ensures that data is securely transmitted and stored.
Furthermore, educating users on data privacy includes informing them about compliance with data protection laws. Users should be familiar with the relevant regulations, such as the Family Educational Rights and Privacy Act (FERPA) in the United States, and understand their responsibilities in adhering to these laws.

Implementing Data Backup and Recovery Plans
Implementing data backup and recovery plans is crucial for ensuring the security and availability of student data in cloud services. In the event of data loss or system failures, having a robust backup and recovery strategy can help educational institutions quickly restore student data and minimize disruptions to the learning process.
Here are four key reasons why implementing data backup and recovery plans is essential:
- Protecting against data loss: By regularly backing up student data, educational institutions can safeguard against accidental deletions, hardware failures, or cyberattacks that may result in data loss. This ensures that valuable student information is not permanently lost and can be easily recovered.
- Enabling data restoration: A comprehensive backup and recovery plan allows educational institutions to restore student data to a previous state in the event of data corruption or system failures. This ensures that educational processes can continue seamlessly without significant disruptions.
- Ensuring data availability: Data backup and recovery plans help ensure that student data is readily available when needed. In case of any unforeseen circumstances, such as system outages or natural disasters, educational institutions can quickly restore access to student data and continue providing uninterrupted services.
- Complying with regulations: Implementing data backup and recovery plans is not only essential for security but also for compliance with data protection regulations. By having a robust backup strategy in place, educational institutions can demonstrate their commitment to protecting student privacy and meeting legal requirements.
Monitoring and Detecting Suspicious Activities
Effective monitoring and detecting of suspicious activities is crucial for ensuring the security of student data in cloud services. By continuously monitoring user activities, system logs, and network traffic, organizations can identify and respond to potential security threats promptly.
One approach to monitoring is the use of Security Information and Event Management (SIEM) systems, which collect and analyze log data from various sources to detect anomalous behavior. These systems can help identify unauthorized access attempts, data breaches, or unusual patterns of activity that may indicate a potential security incident.
In addition to SIEM systems, organizations can also employ intrusion detection and prevention systems (IDPS) to monitor network traffic and detect any malicious activity. IDPS can analyze network packets in real-time, looking for signs of unauthorized access, malware, or suspicious behavior. By using signature-based detection or behavior-based analysis, these systems can detect known threats and identify potentially new or emerging threats.
Furthermore, organizations should implement user behavior analytics (UBA) tools to monitor user activities and identify any abnormal behavior that may indicate a compromise. UBA tools analyze user behavior patterns and can detect anomalies such as excessive data access, unauthorized access attempts, or unusual login times and locations.
Regular auditing and review of system logs, user access logs, and authentication logs are also essential for detecting suspicious activities. By analyzing these logs, organizations can identify any unauthorized access attempts, privilege escalation attempts, or suspicious user activities.

Frequently Asked Questions
How Can Cloud Service Providers Ensure the Security and Privacy of Student Data?
Cloud service providers can ensure the security and privacy of student data by implementing robust encryption protocols, regularly updating security measures, conducting thorough risk assessments, and adhering to data protection laws and regulations.
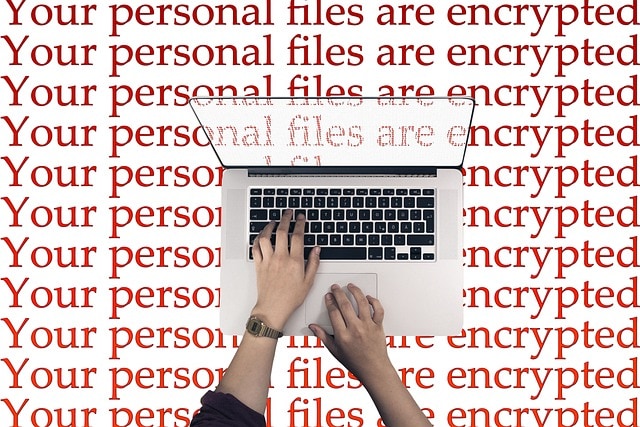
What Are Some Common Vulnerabilities or Risks Associated With Cloud-Based Student Data?
Common vulnerabilities and risks associated with cloud-based student data include unauthorized access, data breaches, lack of control over data storage, potential for data loss, and non-compliance with data protection laws, highlighting the need for robust security measures and encryption protocols.
Are There Any Specific Data Protection Laws or Regulations That Schools or Educational Institutions Need to Comply With?
Schools and educational institutions must comply with specific data protection laws and regulations to ensure the security and privacy of student data. These laws vary by jurisdiction and may include requirements for data encryption, access controls, and breach notification.
How Can Educational Institutions Ensure That Their Cloud Service Providers Are Using Strong Encryption Methods to Protect Student Data?
Educational institutions can ensure that their cloud service providers are using strong encryption methods to protect student data by conducting thorough due diligence, requiring contractual obligations for encryption, and regularly auditing security measures to ensure compliance.
What Measures Can Be Taken to Prevent Unauthorized Access to Student Data Stored in the Cloud?
To prevent unauthorized access to student data stored in the cloud, measures such as strong authentication mechanisms, role-based access control, regular security audits, and implementing data loss prevention strategies can be taken.
Conclusion
In conclusion, securing student data in cloud services is of utmost importance for educational institutions. By implementing strong access controls, regularly updating security measures, and conducting thorough vendor assessments, schools can enhance their data security practices.
Additionally, educating users on data privacy, implementing data backup and recovery plans, and monitoring suspicious activities are crucial steps in protecting and maintaining the confidentiality of student information.
These strategies, when combined, create a safe and secure digital learning environment that fosters academic success.
