Hola Free VPN is a popular free virtual private network (VPN) service that provides users with internet privacy and anonymity. However, recent reports have revealed…
Enforcement of Cyber Laws by Nikoloz Kokhreidze
Enforcement of Cyber Laws In 2014 I wrote an award winning article about enforcement of cyber laws. On November 4th I was awarded a prize for…
Best Virus Protection
Introduction Let’s face it. Today cyber attackers are so sophisticated that an advanced attacker can bypass any even best virus protection and successfully initiate attack. Shortly…
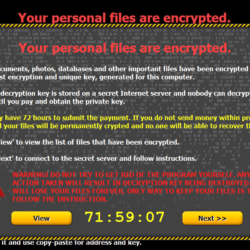
The Best Ransomware Removal
In the previous article we discussed the new PolloCrypt, Breaking Bad ransomware and showed you how it works. But today we provide you with the…
How to Protect Yourself from LogJaM Vulnerability
Introduction A Logjam vulnerability has been uncovered yesterday. The Logjam flaw, just like FREAK, is present in TLS (Transport Layer Security protocol) that is responsible…
Pollocrypt New Breaking Bad Ransomware
Ransomware is a type of malicious software that encrypts the data on a victim’s computer and demands payment in order to decrypt it. Pollocrypt New…