The Panama Papers is a group of 11.5m files (2.5 terabytes of data) which were leaked from the database of the world’s fourth-biggest offshore law firm, Mossack Fonseca. The records were obtained by the German newspaper Süddeutsche Zeitung from yet anonymous source. The newspaper has shared them with the International Consortium of Investigative Journalists (ICIJ). The ICIJ then shared them with a large network of international partners, including the Guardian and the BBC. Panama Papers holds proofs and shows us how rich can exploit secretive offshore tax regimes and how the most influential people of our times are involved in corruption.
For now, it is not officially clear how the database was leaked…was it hacked? was this an insider job? We don’t know for sure, but what we know is that one of the WordPress plugins might be the cause. Guys at Wordfence, security plugin for WordPress, has published an interesting finding, about a vulnerability in Revolution Slider. According to their blog post the Panamanian law firm may have been breached via a vulnerable version of Revolution Slider.
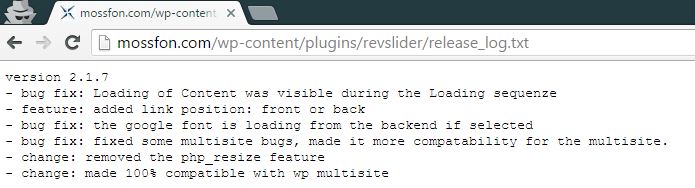
Wordfence has conducted the analysis of the Mossac Fonseca website and discovered that it was running a WordPress with a vulnerable version of the Revolution Slider plugin, which allows crooks to gain shell access to the server. On the link [ ] we can see version 2.1.7, while most recent one is 3.0.95.
What does a WordPress security guy do after discovering a vulnerable plugin on a website? No… he does not call the police, he checks if it is exploitable. And that is exactly what Wordfence guys did, they decided to investigate further and found out that:
- Before the breach, their IP was on the same network as their mail servers and it was not even behind a firewall.
- One of their IP’s run MS Exchange 2010
- They use VPN
- IP addresses used for email
- They were serving sensitive customer data from their portal website which includes a client login to access that data.
Here is a demonstration of the vulnerability:
Tools used: Shodan, Netcraft, ViewDNS
Source: Mark from Wordfence