PUMA virus is a type of ransomware that can cause a lot of trouble for individuals and companies. If you are unfamiliar, here’s a quick intro covering how ransomware works and how PUMA takes control of your important files.
This will help you understand the basics before you focus on how to remove the virus.
What Is Ransomware?
Ransomware is a form of malicious software which enters your PC through emails, flash drives or downloaded torrent files. It arrives without the user’s knowledge and then runs in the background undetected.
Once installed, it encrypts files, documents and folders, and then demands a ransom before allowing you to regain access. However, there is of course no guarantee that you will actually regain access should you pay the ransom.
PUMA Ransomware Virus: How Does It Infect and What Does It Do?
Here’s a quick overview of PUMA and its functions:
- PUMA ransomware is a data locker virus, which tries to dupe users into opening a spam email message.
- Most users confirm that it gets sent in the form of a shipping company email, like one from FedEx or DHL with a .doc Word attachment.
- When you open the file, it will immediately start running in the background and encrypt most files, including spreadsheets, documents and presentations, with the exception of the core Windows files that keep the PC running.
- Typical STOP ransomware such as PUMA is used to extort money ranging between $500 to $1,500 in Bitcoins, even more in some cases.
How to Remove PUMA Ransomware in Windows Safe Mode
- Click and hold the Windows key, then press R.
- It will open the Run dialog box in which you should type msconfig.
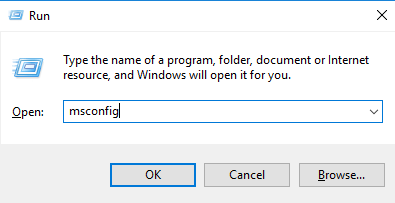
- Press enter to open the Configuration box and click on the tab that says Boot.
- Use the dialog box to select Safe Boot and make sure to head to the Network to tick it.

- The options will restart the computer in Safe Mode with Networking enabled.
How to Manually Open Hidden Files and Delete Malicious Files
The process is quite similar on Windows 7, Windows 8 and Windows 10. However, the steps are all described for Windows 10, which is the latest operating system, and you will be able to do the same on older versions as well.
- Open the folder and find the option View. You will find a couple of checkboxes on the right-hand side.
- Find the option Hidden Items and tick it to show all hidden files.
- Click Apply.
- Remove malicious hidden files manually by browsing through different file folders.
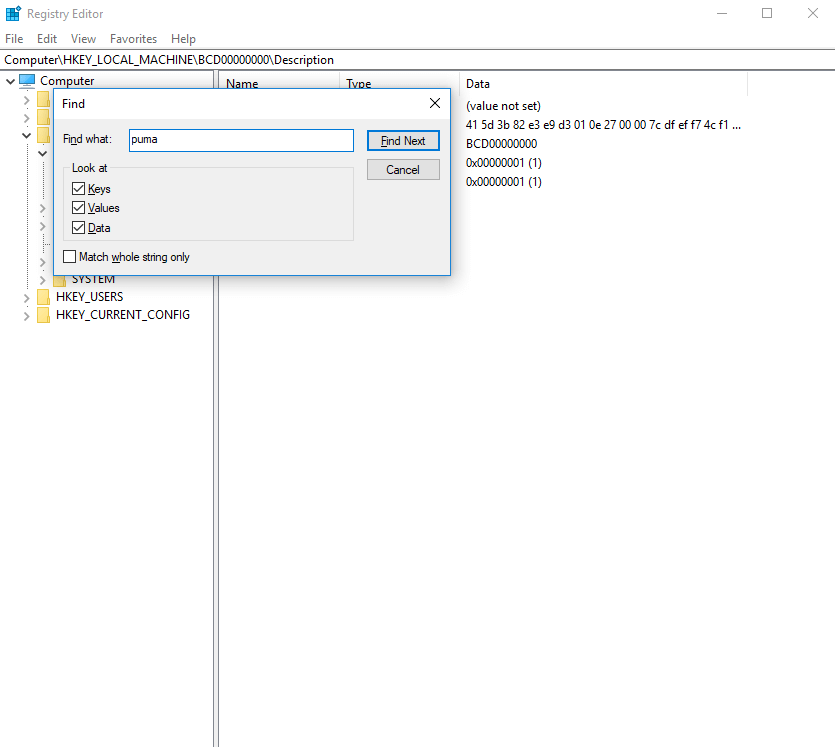
Steps to Repair Windows Registry After Removing PUMA Ransomware
- Open the run command (Hold your windows key and click on R to open it).
- In the open dialog box, type regedit. A long list of processes and registry entries will open.
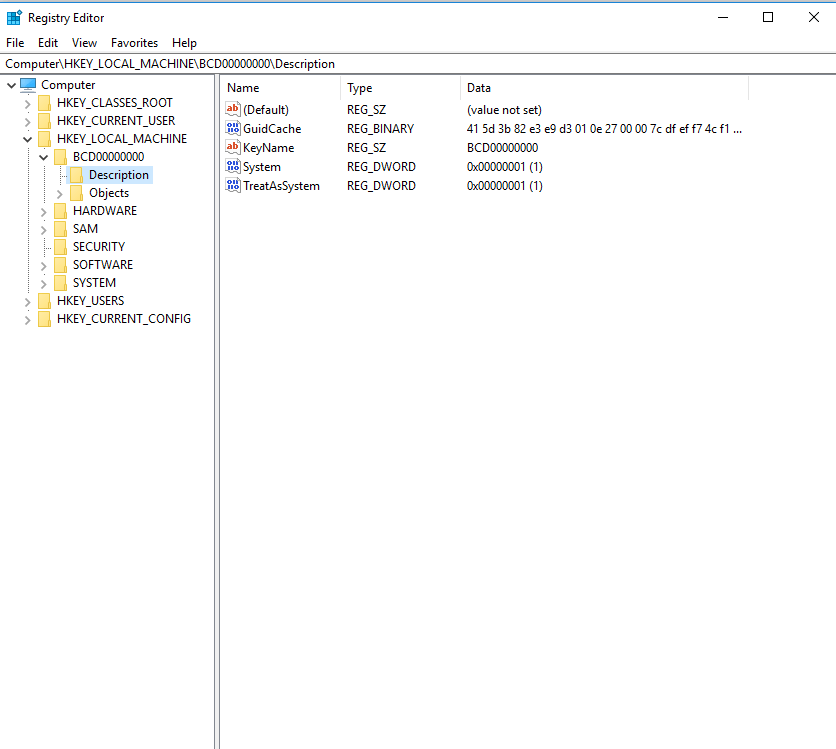
- Use Ctrl + F to trigger the search box in which you should type puma, pumax and pumas to cover all variants.
4. All files associated with the name will automatically be highlighted so that you can remove them all from the registry.
Removing PUMA from the Task Manager
In order to take control of the entire PC, any ransomware, such as PUMA, will try to run in multiple locations and stay hidden inside folders. If you want to delete it manually, you should do it step by step in all locations. The task manager often displays a long list of active processes and it is one of the important areas where a malicious program could be lurking.
- On Windows 10 computers, press CTRL + Shift + Esc which will directly open the Task Manager. The process is the same for Windows 8 and Windows 7 as well.
- Among the different tabs you find, identify Processes and search in it to find anything related to PUMA.
- Identify any running processes that look suspicious. PUMA often runs in Task Manager under the name exe (32-bit).
Decrypt Your Files with Shadow Explorer
Most PC enthusiasts know about Shadow Explorer, a software that creates shadow copies of your computer and will allow you to go back to a previous version. Shadow Explorer works on all versions of Windows including 7, 8 and 10.
Open the program and follow the instructions to decrypt your files by going back to their previous versions saved prior to the malware infection. Some ransomware programs delete these shadow files by gaining administrator privileges, but it doesn’t hurt to try it once.
Using Popular Data Recovery Tools to Recover Deleted Files
The process behind data recovery tools is very simple—it helps bring back deleted data. Ransomware tends to convert existing files into the encrypted format and sometimes deletes the original files once encrypted.
- Try popular data recovery software such as Disk Drill, TestDisk or Recuva. One of these programs should help recover some or all of your files without paying a ransom.
- When the process is complete, save all your recovered files in a different hard drive.
- Run an antivirus software program to clean up your disk. A fresh installation of the Windows OS should help as well.
Proactive Steps to Protect Yourself Against PUMA Ransomware

Removing ransomware like PUMA can be tedious and tiring because hackers often use the highest level of encryption technology to take control of users’ files.
While deleting the ransomware, though you may remove it from your PC, there is also still a chance that your files may get deleted or corrupted. But there are ways to avoid this.
Users with small yet critical files can buy cloud storage space to keep a backup copy online at all times.
Data recovery software can help in some scenarios but if you have large video files or other files, be sure to keep a copy on a local server that is not connected to the internet.
Such measures safeguard you against PUMA attacks and ensure your files are backed up. Finally, never open documents in emails from unknown sources.