
The usage of mobile devices for accessing the internet started years ago. However, now, an overwhelming share of people use only mobile devices in preference to laptops and PCs.
Mobile devices were initially used for just messaging and making voice calls; now practically every activity that one could do on larger screen devices can be done on mobile operating systems.
Mobile device manufacturers, too, have supported the trend by launching smartphones with larger display screens, fulfilling the requirements of the users for watching videos and playing games.
But, with this trend comes all the risks associated with any connected device. Hackers have developed malware specifically designed to attack mobile operating systems.
It is therefore essential that all users of smartphones or tablets first understand the scope of the risk their devices can be exposed to and then take the steps needed to avert any breach in their devices’ security.
Malware Attacks Through Apps
There are broadly only two types of mainstream mobile devices; the ones which run on Google’s Android and the ones with Apple’s iOS. Now the general sense is that the iOS devices are more secure than that of Android, whatever may be the underlying reason.
But almost 90 percent of the devices in the global market run on Android. Discussions on malware here are mostly applicable to Android phones rather than to iOS devices.
The hackers precipitating these attacks employ many methods to carry the malware into the device. In PCs, it used to be through phishing emails. A malware carrying attachment to an email used to be the method.
But, with the advent of the smartphones, apps are a great boon to these unscrupulous elements. They manage to plant malicious apps in the Google Play Store. The apps, by themselves, may be clean, but the ads within the app can lead you to a webpage that has malicious content in it.
Apps can be risk-laden in a mobile device. Within this risk, you can count the potential for adware, a term coined from malware and advertising.
Any number of advertising you see on your mobile screen can be potentially dangerous. You will have to be extremely cautious while clicking on these ads.
Types of Malware
Trade has assigned names to the different types of malware found on mobile devices.
- Adware has been briefly covered above. Adware is basically planting an ad; clicking on which, the user can be led to a high-risk website they should avoid visiting.
- Banking malware, as the name suggests, is the one meant to steal information on banking passwords, credit card details and other such vital personal information to be used to cause loss later.
- Then, there is the SMS malware. Here, the hacker would use the victim’s mobile number to send commercial messages which are charged by the mobile service provider. The user may be unaware that their device is being misused.
- And lastly, Trojans and spyware are also tools used by the hackers to inflict damage on victims’ mobile devices.
Ways to Protect Your Mobile Devices
- Keep Your Phone Locked
Most modern telephones have addressed certain security issues by introducing locking and unlocking systems. The really high-end phones have facial ID unlocking systems while a large number of models have fingerprint sensors to unlock your device.
This ensures that your mobile phone remains what it was originally meant to be—a personal hand-held device. Unless you permit, it cannot be used by anyone, and even if your mobile phone gets stolen, it is not easy to unlock.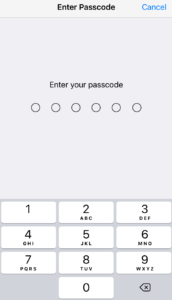
But, from your end, you must make sure you have chosen the settings on your phone to enable locking of the device when not in use for a few seconds and then unlocking through your facial ID or using your fingerprint. If your mobile phone has a passcode to unlock it, make sure you get a strong one that cannot be cracked.
- Can You Encrypt the Contents?
Check if your smartphone has the feature where the important data stored in your device can be encrypted. Encrypting data ensures that even in the worst-case scenario of your phone reaching the hands of some unscrupulous elements, they cannot access the information in it.
But, do make sure you have kept a copy of the information elsewhere, either on secure cloud storage or a removable storage, but not left within the device.
- Install a Good Antivirus

Antivirus software developers have dedicated versions meant for mobile devices. Even the most popular and reputable brands have them. You can choose the right option for you and install it on your mobile device. It will do a periodical scan of and clean up the system if needed. When you are browsing the internet or checking your emails, the antivirus will be there to warn you of any risks.
- Get a Mobile VPN
This is another security provision that you can use to protect your mobile device. A VPN (or virtual private network) acts as the shield to keep the hackers away from your device.
There are mainly two simple things a VPN does—it encrypts data the moment it leaves your device so that it cannot be read on its way and it also hided your phone’s IP address, the unique URL assigned to devices while accessing the internet.
Using a VPN service will further protect your device from being exposed to hackers.
——————–
Ultimately, mobile devices can stay secure as long as you strictly adhere to the basic rules of cybersecurity, as outlined above. The key things to do, as outlined, are to keep your phone locked and ensure it can be opened only by you, and to exercise caution when checking emails, particularly if it is from sources unknown to you and if there are suspicious attachments.
If you are doing banking operations from your financial institution’s app, make sure you enable two-stage authentication to prevent hackers from misusing it.
