How BitTorrent Mitigated DRDoS Vulnerability In previous week we published an article about how it was possible to initiate a BitTorrent DRDoS attack using UDP…
Category: Cybersecurity
NSA Switches to Quantum-Resistant Algorithms
NSA Switches to Quantum-Resistant Algorithms As world is getting near to use of quantum computing security agencies are taking a notice. NSA recommends companies and…
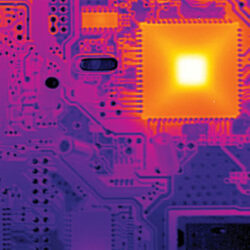
Hacking into Air-Gapped Systems
Hacking into Air-Gapped Systems takes Hacking Into a Whole New Level Generally speaking, we might think that a system cannot be hacked unless it is…
How to Download Ashley Madison Torrent?
Torrents, also known as peer-to-peer file sharing, are a type of distributed network that allows multiple users to upload and download files from one another….
Cyber Security Career at Security Zap
Security Zap is online platform for cyber security and information security research and analysis. We provide daily updates about trending issues and help newcomers to advance in…
Initiating BitTorrent DRDoS Attacks
Using BitTorrent for DRDoS Attacks Researcher Florian Adamsky, City University London; Syed Ali Khayam, PLUMgrid Inc.; Rudolf Jäger, THM Friedberg; Muttukrishnan Rajarajan, City University London have published an…