
When it comes to securing Virtual Machines (VM Security), physical vulnerabilities in memory chips is the Achilles heel amongst all the potential weaknesses currently existing in the cloud computing niche.
One of most painful hardware security exploits seen last year was Rowhammer, which was directed towards DRAM. As per the research carried by Mark Seaborn and Thomas Dullien, rowhammer technique works by repeatedly accessing memory rows in DRAM devices to flip bits in adjacent rows as per the post published on the Google Project Zero Blog.
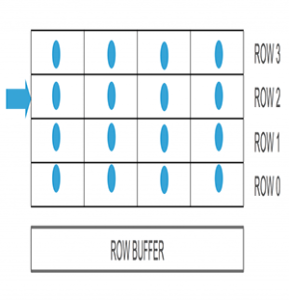
A row hammer is when a program floods a particular row of bits multiple times with data. This hinders the memory controller’s refresh process, causing electrical charges to leak to neighboring rows of bits on purpose, manipulating data that an executable program wouldn’t normally have access to.
Until now Rowhammer was a somewhat unpredictable attack since it had near to zero chance of controlling exactly where the data-corrupting flips happened. Due to the odds of data leakage, privilege elevation, potential hijacking and other multiple reasons – the attack was considered largely a matter of chance.
Now security researchers from VUSec, have revealed a variant of the attack which shifts bits in the memory page of a VM running on the same plane (host) where the attacker’s VM is running. They call this refined Rowhammer “technique” Flip Feng Shui. As per VUSec, it relies on a hardware vulnerability for flipping a bit and a physical memory messaging primitive to land a victim page on the vulnerable physical memory location.
Today, most cloud service providers save memory resources by sharing identical chunks of data used by multiple VMs through deduplication operations and since Flip Feng Shui manipulates these operations, the impact is catastrophic.
RowHammer’s extent of damage
The research team also showed how an attacker VM can use this technique to compromise RSA cryptography keys stored on another VM hosted in the same plane. As per the research paper, they produced a new public key by bit-flipping the in-memory public key then computing the matching private key.
So they have in effect, created their own key pairs of the public / private key which then used it to log into the server. The original private key was never stolen as such. One of the other cases also showcased a malicious virtual machine gaining unauthorized access to a co-hosted victim Virtual Machine by compromising the cryptographic key used to authenticate SSH access.
In a different computing environment, they also were able to compromise the GPG key (used by developers of Ubuntu OS to verify the authenticity of updates). With the compromised GPG they have a control to force the victim to downstream malicious updates.
The researchers in their paper titled “Flip Feng Shui: Hammering a Needle in the Software Stack” wrote, “We find that, while [Deduplication Flip Feng Shui] is surprisingly practical and effective, existing cryptographic software is wholly unequipped to counter it, given that ‘bit flipping is not part of their threat model,’”.
Currently, many servers are using multi-bit Error Correcting Code (ECC) that can recognize and correct multiple bit RAM errors. HP calls their multi-bit ECC “Advanced ECC” and it’s the default mode.
Currently one of the elements which are unclear and not proven is whether the attacks presented by the researchers will work on servers equipped with the DRAM Error Correcting Code. The effect of Rowhammer on ECC has not been well researched by security groups publicly.
There are many tests currently available online for checking whether your DRAM is vulnerable against Rowhammer, for example, memtest86.
