Proxy sites are very popular these days. Many governments tend to censor communications. Even in workplaces, some companies are blocking different internet resources. There are…
Mac Malware: The First Firmware Malware for Mac
Mac Malware: The First Firmware Malware for Mac Mac OS has long been “accused” of being one of the two most secure operating systems, however…
INTERPOL Cyber Crime DIvision: Training Police to Fight in The Darknet
INTERPOL Cyber Crime Division Is Training Police to Fight Crime in Darknet Deep web, Darknet, Tor and other anonymity services have long become an interest…
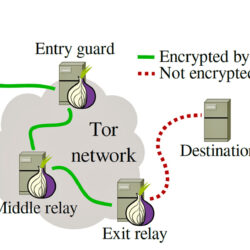
MIT Researchers Break TOR Anonymity Without Cracking Encryption
MIT Researchers Break TOR Anonymity Without Cracking Encryption The fact that Tor is used by millions of users, trying to protect their privacy, on daily…
Hacking Sniper Rifle Using WiFi
Hacking a Sniper Rifle Using WiFi Security researchers Runa Sandvik and Michael Auger have shown Wired a way to break into the rifle and shut it…
Bitdefender Hacked, Customer Data Stolen by Detox Ransome
Bitdefender, a leading provider of cybersecurity solutions, was recently the victim of a major cyber attack. Sensitive customer information was stolen from the company’s secure…