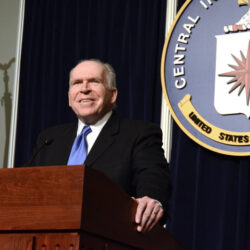
The New York Post reported that a teenager from American High School was able to break into CIA Chief’s John Brennan’s private e-mail account. The magazine was…
Cyber-Warfare: Offensive Versus Defensive Balance
Cyber-warfare is an ever-evolving form of global conflict which involves the use of computer networks and technology to conduct offensive or defensive operations. With the…
The Definition and Benefits of Private Cloud Computing
Private Cloud Cloud computing allows corporate to use a network of remotely hosted server, located on the Internet. This technology evolution has enabled companies to…
Siri and Google Now Hack: Hackers Control Your Virtual Assistants
Siri and Google Now Hack – a report comes from french cyber security researchers who discovered a way to control Siri and Google Now from…
Dell Buys EMC for $67 Billion
Today we are witnessing the biggest technology acquisition of all time as Dell is buying EMC for whooping $67 Billion. EMC may not be the…
What You Need to Know about Secure Server
What You Need to Know about Secure Server The Internet allows people to communication and does all sorts of transactions. The Internet has opened all…