Security researcher Sean Cassidy has discovered a LastPass phishing attack, which would allow an attacker to steal a LastPass user’s email, password, and even two-factor auth code, giving full access to all passwords and documents stored in LastPass.
The attack is conducted thanks to a simple LastPass feature – browser notification.
Users can’t tell the difference between a fake LostPass message and the real thing because there is no difference. It’s pixel-for-pixel the same notification and login screen.
Since the notification is displayed in browser viewport attacker can display a fake notification which looks exactly like LastPass’s original.
How does the attack work?
A victim visits a malicious website or a real website vulnerable to XSS. An attacker deploys a script lostpass.js from Github. The script will check if users have LastPass installed and will pop-up a login expired notification asking users to re-login. LastPass has a Cross-site Request Forgery (CSRF) vulnerability allowing any website to log users out of the extension.
After the notification is clicked users are transferred to a well-known LastPass login page
After victim enters credentials, an attacker will use LastPass API to check the validity of entered information via his own servers. In case if entered username and password are not correct, attacker will redirect the user back to the website and will display an Invalid Password notification.
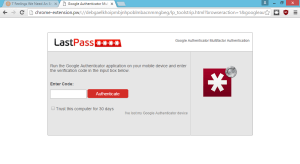
If user has a two-factor authentication enabled, they will be redirected to the two-factor authentication page:
Once the attacker has the correct username and password (and two-factor token), download all of the victim’s information from the LastPass API. Attacker can install a backdoor in their account via the emergency contact feature, disable two-factor authentication, add the attacker’s server as a “trusted device” and much more.
Sean Cassidy published this information on his page.



so, Sean, if I disable my last pass notifications setting , this will close that backdoor hack possibility…am I tracking this write right… Just no substitute fore smart virtual masking . If somebody in genius gets in, all they get is what they are given .. A virtual reality sandbox, custom designing them, A.I. (Actual Intelligence that has reverse hacked them , tagged the mm , and can track them at your mercy , mercy me!!!…NO HACK CYBERWARE < meet Crypt the Gypsy Security Council Chief, And Geniiieee, The masking wiz , with tracking info customized with JDK,mp5, Xplat. Sig.Mirror , no false sig. Ever generated…R YUV With Me!, Sean.. Get in touch for more details, on your next app!!Parlez-Vous DEVcais!EH!-Steve Sorry, got carried away for a moment there!.. I started out to rate you 5 stars, but it wouldnt take my rating, so 5 STARS, Sean, excellent excellent excellent, your teaching me!, Serious ,! Am about your , ¨Next App!¨