One of the latest viruses to attack computers is the .djvu file extension virus. It is a newly discovered type of ransomware in the family of STOP malware, which encrypts important files in your system and then delivers a ransom demand in order to decrypt them. However, such decryption is of course not guaranteed.
This article will then give you an overview of this dangerous malware, explain some of the ways the virus may have entered your computer if your system is infected and then provide step-by-step instructions on how to get rid of it.
What Is the .djvu File Extension Virus?
Though the more common way of representing this virus is .djvu, sometimes the upper case DJVU is used too.
As you might expect, the most frequently used method of infection sees the .djvu file extension virus hidden in spam emails or attachments. To a lesser extent, downloads from sites which may not be secure provide another entrance, together with unknowingly clicking on malicious advertisements.
Regardless of how it arrives, the virus’ worst trait is that it doesn’t wait to inflict its damage. Upon infecting a user’s system, it immediately looks for files with different file extensions, including DOC, TXT, PDF, XLS, JPG, PPT, MP4 and MP3, encrypting them before the user has a chance to realize what is happening.
Once files have been encrypted, they cannot be accessed. Instead, there will be a message that informs you all your files have been encrypted and that the only way to access them is by buying the decryption tool and the unique key from the hacker.
However, the message won’t stop at that. The hacker will want you to be sure that they mean business and give you the option of testing out one file as proof of their hold over it. Some users have found that the attackers offer a 50% discount on the ransom amount if users agree to their condition within three days of their posting the message.
Cybersecurity experts and law enforcement alike strongly recommend against paying the ransom demands made by hackers.
Fortunately, it is possible to remove the .djvu file extension virus from an infected system by following the series of steps outlined below.
NOTE: Users should have a good understanding of computer systems before attempting manual removal so that potentially damaging mistakes can be avoided. If you’re not comfortable with using the manual steps below, it’s recommended that you use an anti-malware program that can scan your system and remove viruses for you.
Steps to Remove the .djvu File Extension Virus Manually
- The first step is to restart the computer in Safe Mode from your sign in screen. This is done in different ways depending on the operating system version your computer is running on. NOTE: The default process outlined here is for Windows 8/8.1/10. If your system is on any other version, the steps may vary. Check Microsoft’s support pages for specific instructions.
2. Go to the Power button and click on it while holding the Shift key pressed.
3. The resulting window will have three options out of which you must choose Troubleshoot.
4. Again, the Troubleshoot window will have three options. Choose the last one:
5. In the next window select Startup Settings.
6. The next step is to click on Restart.
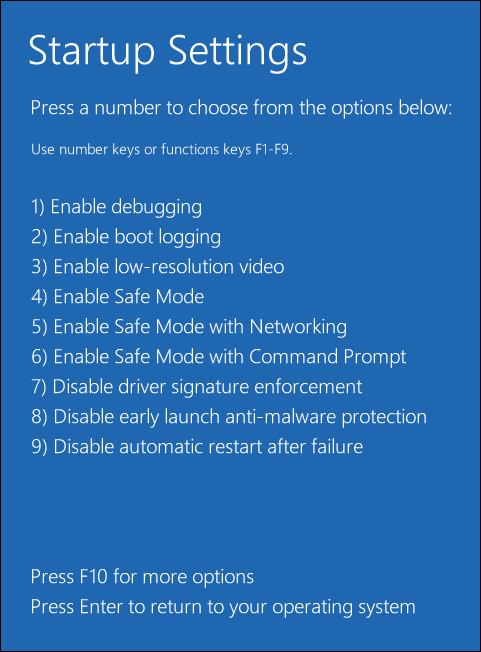
7. The computer will reboot and show a variety of options for Startup. Choose the Enable Safe Mode (There are two more options for Safe Mode, one with Networking and the other with Command Prompt. You can pick any one of these.)
In the next set of steps after the computer has been restarted in the Safe Mode, you will have to search for the offending .djvu file extension virus files and eliminate them. Again here, Windows 10, 8 and 8.1 versions have been used as the example. Steps will vary slightly for different operating systems.
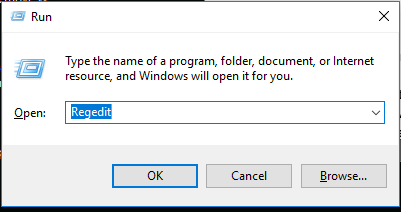
- Navigate to the Run dialogue box by clicking on the Windows and R keys together.
- In the window, type regedit. Then click OK.
3. To search for the files infecting your system, you must seek the search window that appears on the right top corner. Type fileextension:exe and click on the search icon, followed by the file extensions that you want to retrieve. You will need to leave a space between the two. There are a range of extensions that related to .djvu, including .djvur, .djvuq, .djvuu and .djvut.
4. The search bar will have the green band growing horizontally indicating the system is searching for the infected files. Allow it to carry on until the end.
There are other anti-virus/anti-malware programs available which can help you carry out the above identification and removal of the .djvu file extension virus from your computer automatically. That option is always available to you and should be considered before manual removal.
Recovering Lost Files
If you’ve lost files due to the .djvu ransomware, the process of recovering the encrypted files and accessing them as before is not an easy one. If you already have expertise in these matters, you can attempt them.
There are also data recovery software programs available on the market that are designed to decrypt infected files that may be successful. The warning posted by the hacker commands users not to attempt to use any decryption tool to open the files. But that might just be a threat designed to scare people away from utilizing such tools.
You can try using ransomware decryption tools and antimalware programs developed by reputable cybersecurity firms. These decryption programs are available online, usually for free. Before you try this method, though, make sure you’re downloading the decryption tools from reputable and verified sources, like the official websites of cybersecurity software companies.
Protecting Yourself from Viruses like .djvu
The bottom line, as always with viruses, is that you must prevent such attacks on your computer in the first place. If you provide your computer with the appropriate protection from the very beginning, you will not have to face the embarrassment of your important files being hijacked by a virus like the .djvu file extension virus.
The golden rule here is to watch your steps while you are checking your emails. Maybe it’s time to review the process you follow.
For example, be very cautious when opening files and attachments delivered through email addresses you don’t recognize. Check to see who the message is from. If you know the sender and if the attachment still looks suspicious, don’t download the attachment right away. The same applies to downloads.