
Victims of ransomware attacks generally end up paying the ransom the hacker demands so they can retrieve their encrypted files and data.
This trend is evident in cases associated with the recent Everbe ransomware.
But a couple of researchers who specialize in ransomware have found a way to decrypt your locked files and get away without having to pay the ransom. What’s more, they are giving this tool away for free.
If you were to ever find yourself struck in a jam where some unscrupulous elements have managed to break into your system using Everbe and encrypt important documents in your file setup, read on to find out how you can break free from the attack.
How Everbe Works
Once the hacker succeeds in entering your system, the first task they carry out is to encrypt your files. If the hacker knows what kinds of files in your system are quite crucial for you and you would be willing to part with any sum to regain access to them, then they may target only those files; otherwise, whatever files in your system and whichever drive they may be sitting on, would all be encrypted in code and you can neither open them nor use them.
In this case, all files in your folders would have been encrypted and the files will have extensions reading: “.everbe” or “.pain” or “.embrace.”
There would be a Notepad message in the folder which will say, “If you want restore your files write on email everbe.airmail.cc.” It then advises you to “write id-de9bcb” in the subject of the email.
Download the Decryptor Tool and Restore
The decryptor tool, developed by researchers Michael Gillespie and Maxime Meignan, has to be downloaded to enable the next process. You can get it here.
One basic condition for the restoration of the encrypted files in this process is that the original unencrypted version of the documents has to be available on your system.
Without the original version, it is not feasible to decrypt the affected files.
The procedure is as below:
- Go to Settings.
- Click on “Bruteforcer.”
- On this dialogue box, there will be the instruction to “use the original/encrypted pair.”
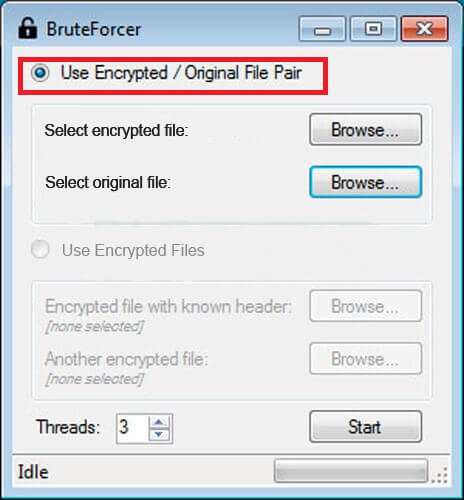
- You will have to select the files one by one.
- Then click on the “Start” button on the same window.
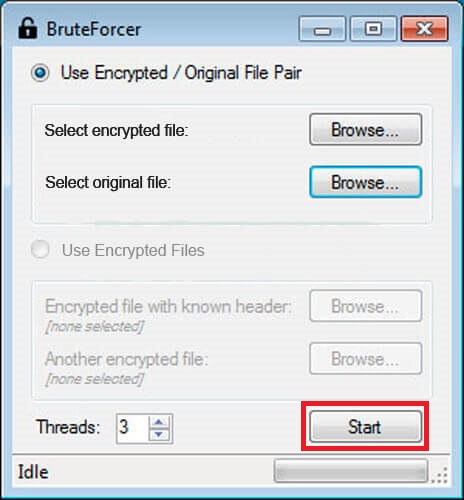
- This will set in motion the process to decrypt your file.
- If there are more files, then you will have to keep selecting them all one by one and then repeat the process again and again.
- When the process is successfully completed, then the downloaded decryptor will announce that a tool has been found.
- At this stage, you will have to close the window by clicking the “x” in the top right. This will result in the key being displayed inside the window.
- Once the key is loaded, it will ask you to spell the directory to which the decryption is to be executed.

- Depending on your situation, you will select the directory necessary to complete this step. If it is a whole drive that has to be decrypted, then click on the whole directory.
- Now click “Decrypt.”
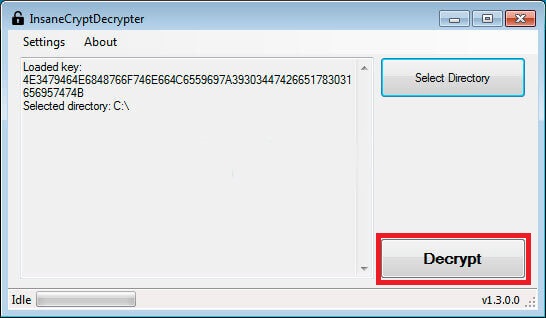
- When the decryption process is completed, the window will present the complete list of files that have been decrypted, so you will know if you got them all
Removing/Isolating the Encrypted Files
Now, having ensured that you have escaped the ransom and have regained access to all your files and documents on your system, you must remember that the files encrypted by the hacker are still inside your computer and you will have to take care of them.
For this process, there is a tool called CryptoSearch developed by the makers of the ID Ransomware service.
Once downloaded and installed in your computer, the tool can conduct a thorough search for any encrypted files and it can then be used to isolate them and put them in a separate folder.
If you are keen on getting rid of the encrypted files completely, then you should first save all your restored documents to a separate external drive.
Once you are sure they are safe, you must clean up your hard disk and reload the OS. This will make it certain that you are out of the encryption saga totally.
Take Care of Your Anti-Malware Status

It may be true that even if you have the best of antivirus program installed on your system, a hacker may still find a way to break in. But that cannot be the reason for you to lower your guard.
You should have the best anti-malware program installed on your system.
Have an expert periodically check if the program is fully updated and working.
Additionally, if your hardware and software providers send you system updates and patches, make a habit to download and install them.
Some people turn off the automatic update option for fear of the system consuming precious data or interfering when they are doing important work.
If you want to do this, you should ensure you check manually for updates and download them immediately once they’re available.
The other breach method used by hackers and those involved in cyberattacks is through email attachments.
Many computer users are aware of the risks involved in opening attachments to the emails in their inboxes unless they are absolutely sure of the identity of the sender. You should also follow the same practice.
Don’t click on any email attachment without questioning its authenticity first, as the attackers know the general tendencies among users and make the email appear legitimate and inviting.
Take these precautions and you can easily avoid becoming a victim of hacking.
