What is Venom Vulnerability? VIRTUALIZED ENVIRONMENT NEGLECTED OPERATIONS MANIPULATION or VENOM vulnerability has been uncovered by crowdstrike. According to senior security researcher Jason Geffner this…
Category: Threat
Cyber Attack on Bundestag
According to Spiegel the national parliament of Germany, Bundestag, has been targeted by a major cyber attack allowing unknown perpetrators to penetrate internal network. According to…
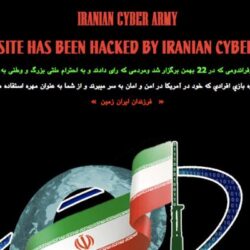
Cyberspace and Cyber Warfare Capabilities of Iran
Introduction Internet is probably the most valuable asset for billions of people all around the world. It plays key roles in our social life, governance,…
Vulnerabilities in Industrial Control Systems – SCADA
Industrial Control Systems (ICS), operate the global industrial infrastructures, such as pipelines, nuclear stations, oil, electricity and much more. ICS comprises Supervisory Control and Data…