The modern world is one of unprecedented connection, where technology has opened new avenues of communication and interaction. Human-computer interaction (HCI) is the study of…
Cloud Computing Explained: Benefits and Challenges
Cloud computing has become a popular solution for businesses to store, manage and process data. This technology provides numerous benefits to users while also presenting…
5G Technology: Speeding Up the Digital Age
The fifth generation of wireless network technology, known as 5G, is rapidly gaining momentum. With more than 3 billion users worldwide expected to have access…
IoT Revolution: Connecting the World Digitally
Like the veins of a human body, the Internet of Things (IoT) connects devices and systems to create an intricate web that is transforming our…
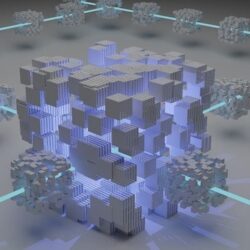
Blockchain Breakthroughs: Transforming Industries
Blockchain technology is like a revolutionary wave that has been sweeping across the digital world over the past few years. It has provided numerous benefits…
AI Demystified: Unraveling Artificial Intelligence (AI)
As the world continues to progress, so does its technology. Artificial Intelligence (AI) has become a major milestone in this advancement, bringing with it countless…