How BitTorrent Mitigated DRDoS Vulnerability In previous week we published an article about how it was possible to initiate a BitTorrent DRDoS attack using UDP…
Category: Vulnerabilities
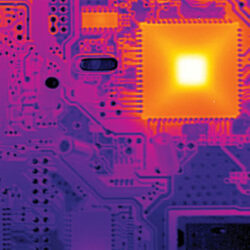
Vulnerabilities are the most important part of security. Discover and fix the most dangerous vulnerabilities
Hacking into Air-Gapped Systems
Hacking into Air-Gapped Systems takes Hacking Into a Whole New Level Generally speaking, we might think that a system cannot be hacked unless it is…
Initiating BitTorrent DRDoS Attacks
Using BitTorrent for DRDoS Attacks Researcher Florian Adamsky, City University London; Syed Ali Khayam, PLUMgrid Inc.; Rudolf Jäger, THM Friedberg; Muttukrishnan Rajarajan, City University London have published an…
Three SAP Vulnerabilities You Need to Patch Right Now
Three SAP Vulnerabilities You Need to Patch Right Now If you are using SAP mobile than your private information is at risk even if it is…
Hackers Install Malicious ROMMON Images on CISCO Devices
Hackers Install Malicious ROMMON Images on CISCO Devices CISCO Product Security Incident Response Team or PSIRT monitors CISCO products for vulnerabilities and attacks and publishes reports…
How to Stay Safe Online Infographics
Staying safe online is an increasingly important topic in modern society. The prevalence of digital technology and the ubiquity of the internet have brought with…