Siri and Google Now Hack – a report comes from french cyber security researchers who discovered a way to control Siri and Google Now from…
Category: Vulnerabilities
Vulnerabilities are the most important part of security. Discover and fix the most dangerous vulnerabilities
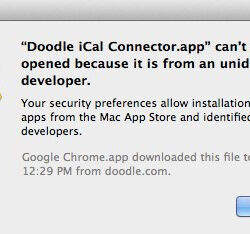
Gatekeeper Hack: How to Bypass Apple Security
Gatekeeper hack allows cyber attackers completely bypass famous Mac security. Using specially crafted exploit cyber attackers are able to open malicious Mac app, even if…
Imgur Used as DDoS Tool Against 4Chan
Today Malwarebytes users might have noticed, that a popular image sharing website Imgur has been blocked by anti-malware software. The reason behind this is that a…
Win $1 Million With iOS9 Exploit
The fact that hackers sell exploits to spy agencies, governments and companies is not a secret. However, September 21, 2015, has made a history. On…
How to Check CISCO for SYNful Knock
How to Check CISCO for SYNful Knock FireEye has discovered a modification of the CISCO’s router firmware image, dubbed SYNful Knock that can be used…
HTTP Malware Analysis Evasion
HTTP Malware Analysis Evasion In this article published by NOXXI.de author explains that are possible using HTTP evader. The very first version of HTTP protocol was…