Cryptocurrency mining has been embedded into websites and web servers lately, utilizing a visitor’s browser as a vehicle to compute mining transactions. It uses unsuspecting…
Category: Cybersecurity
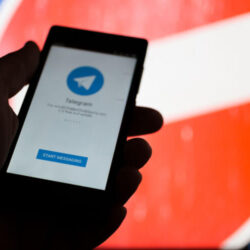
Russia Blocks Millions of IP Addresses in an Effort to Ban Telegram
When messaging apps go fully encrypted, it makes it difficult for governments to monitor the conversations. In an attempt to establish control over its citizens…
Macro Virus – How It Works and How to Remove It
In order to understand the macro virus and how it works, it’s necessary to first examine what the technology is in the first place. Macros…
Almost 50,000 Minecraft Users Infected with Malware
One of the world’s most popular games of the century, Minecraft, has been hit by a serious cyberattack. Reports claim that over 50,000 of its…
Microsoft Outlook Vulnerability Can Allow Hackers Steal Your Windows Logins
Your password to Windows 10 on your desktop/laptop is critical to ensuring your files remain private and cannot be accessed by anyone else. But a…
HTTP Injectors Being Used by Fraudsters to Steal Internet Access
Though most people would expect hackers to come up with new and innovative ways of cheating businesses, very few would have imagined phones with SIM…